Rethink OT Vulnerability Management with Quantified Risk
Power Generation can’t afford generic patch lists. In OT environments—where downtime hits revenue and safety—risk-based vulnerability management outperforms CVSS & EPSS-only sorting. This guide explains how DeRISK Quantified Vulnerability Management (QVM) helps CISOs and OT security leaders prioritize by business impact, not just technical severity.
The Problem with CVE Lists in OT
- Maintenance windows are scarce and patching can disrupt production, or not be available at all.
- A “critical” score doesn’t reflect exploit likelihood, asset criticality or business criticality.
- Teams waste time on low-impact issues while high-risk exposures persist.
What “Risk-Based” Actually Means
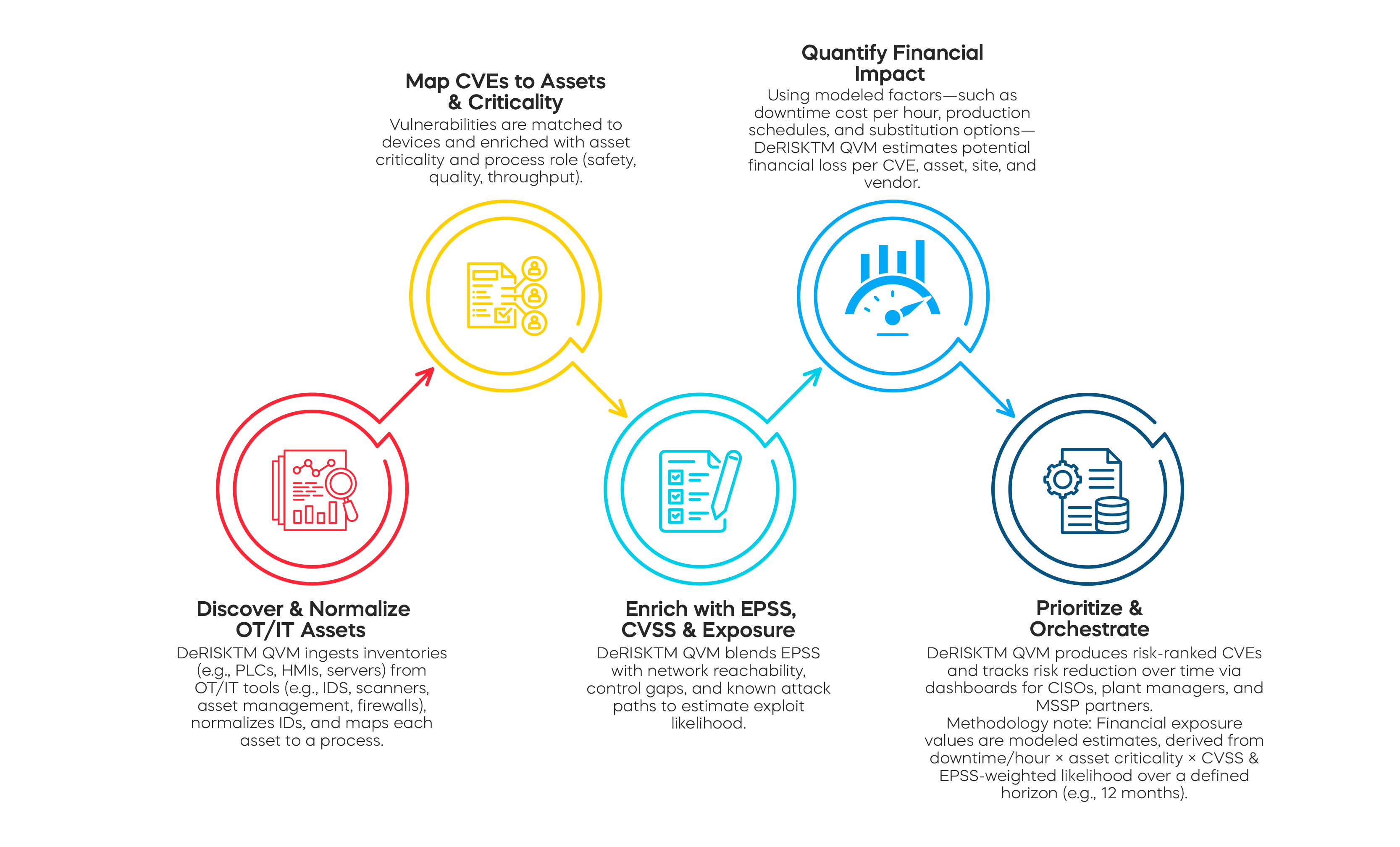
Risk = likelihood × impact. For vulnerabilities, that means blending:
- Exploit likelihood (e.g., CVSS, EPSS, threat intel, active exploits)
- Asset criticality (process importance, safety, revenue)
- Exposure/attack path (network reachability, cybersecurity controls)
- Business impact (modeled financial loss if exploited)
How DeRISKTM QVM Works (Step-by-Step)
Renewable Power Generation Use Case
A leading clean energy developer and operator, assessed its multiple renewable energy plants. Instead of sorting by CVSS & EPSS alone, DeRISKTM QVM identified the highest financial risks and guided limited maintenance windows toward the most impactful fixes.
Example Findings (anonymized, modeled)
|
CVE |
Exposed Devices |
EPSS (est.) |
Total Loss Reduction |
|
CVE -2014-3566 |
378 |
0.94 |
$517,877 |
|
CVE-2013-0006 |
71 |
0.58 |
$297,280 |
|
CVE-2021-44228 |
2 |
0.94 |
$71,447 |
|
CVE-2012-6442 |
35 |
0.21 |
$68,773 |
|
CVE-2017-12542 |
4 |
097 |
$61,634 |
Before/After
Before:
Long CVE list by severity; little clarity on business impact.
After:
Vulnerability insights
- Total CVEs: 10,576
- Distinct CVEs: 389
- Risky CVEs: 83
- 18 in CISA KEV catalog
- Risky / Distinct: 21.3%
- Top 5 CVEs : Drive 72.6% of overall risk
- Top 5 CVEs present in 50 facilities
- 1 CVE in CISA KEV catalog
- Top 5 as % of distinct CVEs: 1.3%
- Riskiest Plants: 2 Solar plants
- Riskiest Devices: Hirschmann switch and Osisoft Historian
-3.png?width=1450&height=727&name=image%20(1)-3.png)
CVSS vs EPSS vs Risk-Based: What to Use When
|
Approach |
What It Does |
Useful When |
Limits in OT |
|
CVSS |
Technical severity based on base metrics |
Quick triage, compliance baselines |
Ignores exploit likelihood & business impact |
|
EPSS |
Probability a CVE will be exploited |
Threat-led prioritization |
Doesn’t include asset criticality or cost |
|
Risk-Based (QVM) |
Combines likelihood + impact (financial) enabling risk-based vulnerability management |
Maintenance-constrained OT, board reporting |
Requires data inputs & modeling assumptions |
Outcomes & KPIs to Track
- Risk reduced ($): delta in modeled exposure post-remediation
- High-risk exposure reduction: % of top-decile items addressed
- Mean time to remediate (MTT-R): prioritized items only
- Actions without patch: % risk reduced via compensating controls
- Time-to-decision: from detection → scheduled change
Implementation Considerations in OT
- Maintenance windows: Coordinate with production; batch changes.
- Vendor constraints: Respect warranties; use vendor-approved mitigations.
- Compensating controls: Network segmentation, allowlists, monitoring.
- Safety & quality: Align with plant SOPs and change control.
Ready to align remediation with business impact? Book a DeRISKTM QVM demo and see DeRISKTM QVM in action.
FAQs
- What is risk-based vulnerability management?
It’s the practice of prioritizing vulnerabilities by likelihood of exploit and business impact, not just technical severity.
- EPSS vs CVSS—what’s the difference?
CVSS measures technical severity; EPSS estimates exploit probability. DeRISKTM QVM uses both alongside asset criticality and financial impact modeling.
- How do I prioritize CVEs when patching is hard in OT?
Use DeRISKTM QVM to target the highest-risk items first and apply compensating controls (segmentation, tuning, monitoring) when patching must wait.
- How do you quantify the business impact of a CVE?
DeRISKTM QVM models potential loss using downtime costs, asset criticality, CVSS & EPSS-weighted likelihood, and exposure paths over a defined time horizon.
- What metrics should CISOs track?
Modeled risk reduced ($), MTT-Remediate for prioritized items, percent of high-risk exposure reduced, and percent of risk reduced without patch.